Post-Quantum Encryption in Fintech Preparing Financial Systems for the Quantum Era
Modern fintech platforms rely heavily on cryptography to secure payments, identities, and financial data. Technologies such as RSA, Elliptic Curve Cryptography (ECC), and Diffie-Hellman underpin everything from mobile banking apps to international payment networks.
However, the emergence of quantum computing threatens to break many of these widely used cryptographic systems. Quantum algorithms such as Shor's algorithm could theoretically solve the mathematical problems that current encryption relies on, rendering today's security models obsolete.
For fintech companies handling sensitive financial transactions, personal data, and payment credentials, this represents a long-term systemic risk.
This is where Post-Quantum Cryptography (PQC) becomes critical.
Traditional cryptography relies on mathematical problems that are computationally infeasible for classical computers to solve.
Examples include:
- Integer factorization (used in RSA)
- Discrete logarithms (used in ECC)
- Elliptic curve cryptography
Quantum computers can potentially break these using algorithms such as:
- Shor's Algorithm - breaks RSA and ECC
- Grover's Algorithm - weakens symmetric cryptography
While large-scale quantum computers capable of doing this do not yet exist, data encrypted today may be harvested and decrypted later once quantum machines mature. This is known as:
“Harvest Now, Decrypt Later”
For financial institutions where data must remain secure for 10-20 years, this threat is already relevant.
Post-Quantum Cryptography refers to cryptographic algorithms designed to remain secure even against quantum computers.
Unlike quantum cryptography (which requires special hardware), PQC works on existing computers and networks, making it practical for fintech adoption.
These algorithms rely on mathematical problems believed to be resistant to quantum attacks, such as:
- Lattice-based cryptography
- Hash-based signatures
- Code-based cryptography
- Multivariate polynomial cryptography
- Isogeny-based cryptography
The global transition to PQC is being led by the National Institute of Standards and Technology (NIST).
In 2022–2024, NIST selected several algorithms for standardization:
Encryption / Key Exchange
- CRYSTALS-Kyber
Digital Signatures
- CRYSTALS-Dilithium
- Falcon
- SPHINCS+
These algorithms are expected to replace RSA and ECC across many systems over the coming decade.
Fintech systems manage some of the most sensitive digital assets and transactions globally. The impact of a cryptographic failure would be catastrophic.
Key areas affected include:
1. Payment Infrastructure
Systems such as card networks, UPI, and real-time payment rails rely on cryptographic authentication and secure messaging.
Quantum attacks could compromise:
- Payment authorization
- Transaction integrity
- Tokenized payment credentials
2. Digital Identity and KYC
Fintech platforms store sensitive identity data including:
- Aadhaar numbers
- PAN information
- Bank account details
- Biometric identifiers
If current encryption becomes breakable, historical identity records could be exposed.
3. Open Banking and API Security
Modern fintech relies heavily on APIs secured with TLS certificates based on RSA or ECC.
Quantum attacks could compromise:
- API authentication
- OAuth tokens
- Secure financial data exchange
4. Blockchain and Digital Assets
Many blockchain systems rely on elliptic curve signatures.
For example, cryptocurrencies like Bitcoin and Ethereum use ECC-based signatures, which could theoretically be broken by sufficiently powerful quantum computers.
Transitioning to post-quantum cryptography is not trivial.
1. Larger Key Sizes
PQC algorithms often require larger keys and signatures.
Examples:
- Algorithm Key Size
- RSA-2048 256 bytes
- Kyber 800-1500 bytes
This impacts:
- Network bandwidth
- Storage
- Latency
2. Infrastructure Compatibility
Financial infrastructure includes:
- Payment gateways
- HSMs
- Mobile SDKs
- Hardware tokens
- Smart cards
All of these may require upgrades to support PQC algorithms.
3. Long System Lifetimes
Financial systems often run for 15-20 years.
Systems deployed today must be quantum-safe for future compliance.
Most experts recommend hybrid cryptography during the transition period.
This means combining classical cryptography with PQC.
Example TLS handshake:
RSA/ECC + Kyber
If either algorithm remains secure, the connection remains protected.
Major technology companies including Google, Cloudflare, and IBM are already experimenting with hybrid PQC deployments.
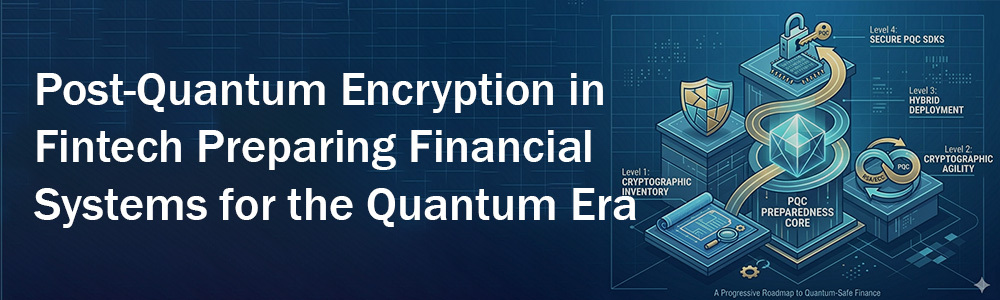
An emerging opportunity in the fintech ecosystem is Post-Quantum Security SDKs.
These SDKs allow fintech apps to become quantum-safe without redesigning their infrastructure.
A typical PQC SDK could provide:
- Post-quantum key exchange
- Quantum-safe digital signatures
- Secure API authentication
- Encrypted mobile communication
- Secure payment tokenization
This approach allows fintech platforms to upgrade security with minimal architectural change.
Financial regulators are already starting to examine quantum-related risks.
Institutions such as:
- Bank for International Settlements
- European Central Bank
have begun discussions on quantum resilience for financial infrastructure.
Over the next decade, regulators may require:
- Cryptographic agility
- PQC migration plans
- Quantum risk assessments
Fintech organizations should begin preparing now.
1. Cryptographic Inventory
Identify where cryptography is used:
- TLS
- APIs
- Databases
- Payment systems
- Identity verification
2. Enable Cryptographic Agility
Systems should be designed so cryptographic algorithms can be replaced easily.
3. Begin Hybrid Deployments
Introduce PQC alongside existing encryption.
4. Upgrade HSM and Key Management
Ensure hardware supports post-quantum algorithms.
5. Prepare Long-Term Data Protection
Sensitive financial data should be encrypted with quantum-safe methods.
Beyond security, PQC also presents an opportunity.
Startups could build:
- Quantum-safe payment infrastructure
- PQC identity verification systems
- Secure fintech SDKs
- Quantum-safe blockchain wallets
- Post-quantum banking APIs
Fintech companies that move early may gain regulatory trust and competitive advantage.
Quantum computing may still be years away from breaking modern cryptography, but the financial sector cannot afford to wait.
Data being generated today must remain secure for decades. This makes post-quantum cryptography one of the most important security transitions in financial technology.
Fintech organizations that begin adopting PQC strategies now will be better positioned to protect customer data, maintain regulatory compliance, and secure the future of digital finance in the quantum era.